CUTTER IT JOURNAL VOL. 29, NO. 7
The IoT Is Everywhere
The Internet of Things (IoT) today covers many areas of our lives. More and more household appliances are becoming smart, with small computing devices and connection to the Web. Smart TVs and refrigerators are already common in many households. There are also smart thermostats (which collect information about the behavioral patterns of the persons living in the home to ensure efficient heating and cooling), smart door locks (which allow their users to open and close their doors from a remote location), smart security systems (which enable remote control of the security sensors), and so on. In the field of healthcare, there are home diagnostic bedside units, which can quickly give measurements for cholesterol, blood glucose levels, and blood pressure, and systems that can remotely monitor patients’ vital signs. Other fields of IoT include autonomous and connected cars, wearable devices, office equipment, and so on.
According to Cisco, there will be about 50 billion networked devices by 2020. The IoT will soon be everywhere.
Vulnerabilities and Risks
Smart Homes and Enterprises
IoT devices have many advantages, but also vulnerabilities and risks. Many smart household appliances are poorly protected (if at all) against cyberattacks. This means that any script kiddie with minimal hacking skills can use them to break into the home network. If, a few years ago, someone had said that TVs and refrigerators could be compromised by hackers to send malicious emails, you would have laughed at them. But such an attack indeed happened on January 2014 — the first known cyberattack to use smart household appliances. This global attack campaign involved more than 750,000 malicious email communications coming from more than 100,000 everyday consumer gadgets such as home-networking routers, connected multimedia centers, TVs, and at least one refrigerator that had been compromised and used as a platform to launch attacks.
In October 2015, a security researcher demonstrated how to hack into a kettle and steal a home’s Wi-Fi password. This vulnerability can be exploited by hackers to break into the Wi-Fi network and from there into the other devices connected to that network. But the risks are even bigger. Researchers have found a way to attack the power grid, by remote manipulation of home and office air conditioners to create a surge. To achieve the hack, attackers target remote shutoff devices installed by utilities on air-conditioning units to preserve power during summer peaks. It seems that these devices are very vulnerable to manipulation by hackers.
Security in the Internet of Everything Era
Explore the existing and future risks in what we currently call the Internet of Things, gain examples of risks and attacks in different domains, and identify the corresponding technological and managerial challenges for confronting — even anticipating and warding against — security attacks. Order your copy of the complete Cutter IT Journal issue today using Coupon Code IOT20 and Save 20%!
To understand how easy it is to hack IoT devices, in March 2016 the MIT Media Lab hosted a hackathon in which it invited 153 hackers to try to find and exploit weaknesses in more than 20 smart home devices.
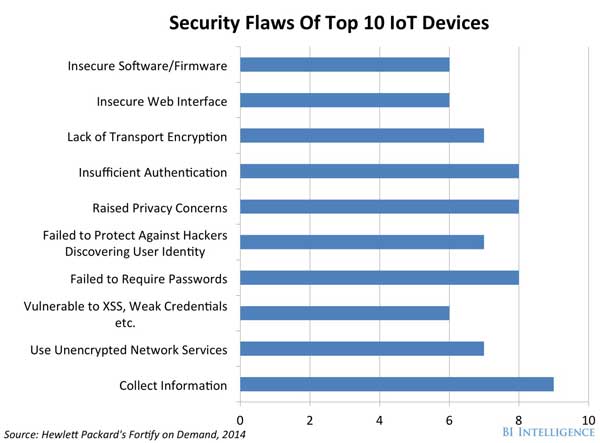
The hackers attempted to control the devices through software vulnerabilities, and they succeeded in taking control of 25% of the devices in less than three hours. Figure 1 depicts the vulnerabilities of the top 10 IoT devices. We can see, for instance, that 8 of 10 such devices use insufficient authentication.
Just as personal computers can be unknowingly compromised to form robot-like “botnets” that can launch large-scale cyberattacks, cybercriminals have begun to commandeer components of the IoT and transform them into “thingbots” to carry out the same type of malicious activity. Cybercriminals intent on stealing individual identities and infiltrating enterprise IT systems have found a target-rich environment in these poorly protected Internet-connected devices, which may be more attractive and easier to infect and control than PCs, laptops, or tablets.
Vehicles, Fuel
Recently, the US Federal Bureau of Investigation (FBI) released a public service announcement to warn drivers about the threat of over-the-Internet attacks on cars and trucks. The announcement mentions that modern motor vehicles often include new connected vehicle technologies that aim to provide benefits such as added safety features, improved fuel economy, and greater overall convenience. Aftermarket devices also offer consumers new features to monitor the status of their vehicles. However, with this increased connectivity, consumers and manufacturers should maintain awareness of potential cybersecurity threats.
Vulnerabilities may exist within a vehicle’s wireless communication functions, within a mobile device (e.g., a cellular phone or tablet connected to the vehicle via USB, Bluetooth, or Wi-Fi), or within a third-party device connected through a vehicle diagnostic port. In these cases, it may be possible for an attacker to remotely exploit these vulnerabilities and gain access to the vehicle’s control network or to data stored on the vehicle. During the “Car Hacking Village” at DEF CON 2015, researchers showed how to hack into a Jeep Cherokee and remotely shut off its brakes and engine.
Criminals can also attack business-critical devices connected to the Internet. For example, using the connectivity of monitoring systems on gas pumps, they could cause the pump to register incorrect levels, creating either a false indication of low fuel level or allowing a refueling vehicle to dangerously overfill the tanks, thus creating a fire hazard. Alternatively, they could hack the connection to the point of sale system, allowing fuel to be dispensed without registering a monetary transaction.
Healthcare
From GPS-enabled asthma inhalers to wearable devices that monitor vital functions, consumer-generated health data can hold value not just for the patients, but for a variety of other parties, such as healthcare providers, insurers, public health researchers, and policy makers. Yet the rise of the IoT coupled with the poor state of cybersecurity within healthcare today makes healthcare-related IoT devices a target for both data theft and extortion. A partial electronic health record (EHR) sells on the black market for roughly US $50, and health credentials can sell for $10 each, many more times the value of a credit card number. The reason is that an EHR can be used to file fraudulent insurance claims, obtain prescription medication, and facilitate identity theft.
In addition, one of the latest trends in ransomware attacks is the targeting of hospitals and other healthcare facilities. As a recent Wired article notes:
Hospitals are the perfect mark for this kind of extortion because they provide critical care and rely on up-to-date information from patient records. Without quick access to drug histories, surgery directives, and other information, patient care can get delayed or halted, which makes hospitals more likely to pay a ransom rather than risk delays that could result in death and lawsuits.
In the case of extortion, just imagine what would happen if data for every patient in a hospital were held ransom.
IoT Exploit Strategies
IoT vulnerabilities can be exploited by cybercriminals in various ways. If an attacker succeeds in hacking a smart home device, they can control the device (think what could happen if the device were a pacemaker), hack into the home’s/organization’s Wi-Fi network, and subsequently hack into the connected computers in order to steal sensitive information, such as bank account passwords, credit card numbers, and private business information. They can also gather information on people’s habits (e.g., when they order pizza, which medicines they take, when they take breaks) and more.
The hacker can use the collected information for spear phishing, showing a fake login page to the user and stealing their credentials, sending an email (with relevant content according to the collected information) with an attachment or a link that will install malware on the user’s device when opened, and so forth.
A recent FBI alert about the IoT points to several additional risks:
- Exploiting the Universal Plug and Play protocol (UPnP) to gain access to many IoT devices
- Compromising an IoT device to cause physical harm
- Overloading IoT devices to render them inoperable
- Interfering with business transactions
What Should Be Done
The risks are clear, so why don’t vendors make an effort to provide more secured devices? The answer is simple: they don’t have to. Vendors naturally want to maximize their revenue. So they focus their efforts on improving the devices’ price, aesthetics, ease of use, fault resistance, and other characteristics that consumers want. Vendors either are not aware of cybersecurity risks or just ignore them, since it’s not cost-effective to handle the risks.
Overcoming this issue will require action from four groups:
- Consumers
- Vendors
- Regulators
- Researchers
Consumers
We should begin by raising awareness among smart appliances’ consumers about the cybersecurity risks. If consumers demand more secured appliances, vendors will have to supply them. In addition, consumers with strong information security awareness may be better protected against social engineering attacks.
Vendors
It is important for vendors to understand that it is only a matter of time until exploiting IoT vulnerabilities will become common, with consequent damage to the vendors’ reputation. Publications about cyberattacks on IoT devices raise awareness on cybersecurity among vendors and consumers. Some steps that vendors can take to improve IoT security include:
- Using open source and open security. The open source community is totally focused on quality and usability. Thanks to the strength, dedication, and sheer size of the open source community, security flaws are routinely fixed within hours of discovery.
- Signing the software in embedded devices. Developers should ensure that the system boots up only if the software to execute is signed by a trusted entity. By anchoring this “root of trust” into the hardware, it becomes extremely difficult to tamper with firmware.
- Separating critical and noncritical systems. Manufacturers try to collapse as many functions as possible within one single piece of hardware, but there’s no real reason why these separate functional domains should be visible to each other. For example, it shouldn’t be possible to access an airplane flight control system via the plane’s onboard entertainment platform, or a car’s brakes and assisted steering wheel from the car stereo unit.
Regulators
We cannot rely on the efforts of consumers and vendors alone. There should be international standardization and regulation to define the standards of IoT security and enforce those standards among vendors. Most large organizations understand the importance of securing themselves against cyberattacks. Small and medium-sized companies, as well as household consumers, need the regulators to protect them. In some countries, riding a motorcycle without a helmet is against the law. Bikers know the danger of not using a helmet, but without laws to enforce it, many riders would not wear one. International regulations should enforce “helmets” for IoT devices.
One might question the viability of international regulation, considering that each country has its own interests. Yet if we extend the road rules analogy, we can observe that while every nation has its own driving rules, there are nevertheless many commonalities. There is no need for complete harmony in order for countries to issue and honor international driver’s licenses. A similar approach should be considered for IoT cybersecurity. Each nation is free to implement its own rules, but there are certain core defense concepts that will play out (with variations) just about everywhere.
In December 2015, the European Union (EU) agreed on the first EU-wide rules to improve cybersecurity. Under the new rules, companies in critical sectors such as transport, energy, banking, financial services, health, and water supply will have to ensure that the digital infrastructure they use to deliver essential services, such as traffic control or electricity grid management, is robust enough to withstand cyberattacks. This directive marks the beginning of platform regulation. We should expect such international regulations to apply to securing the IoT.
Researchers
From the academic side, researchers are trying to identify different building blocks for security improvement. Many IoT devices use Wi-Fi for communication, and researchers have found a way to detect tampering with this type of communication. Traditional cryptographic operations can be used to authenticate data transmitted from IoT devices. However, tampering with a device cannot be detected using cryptographic methods. Using analysis of transmitted data from devices would allow an additional layer of defense that can detect these tampering events.
The issue of IoT security is also the subject of international conferences. The executive summary of Cyber Conference Okinawa 2015 argues that it is essential to determine an architecture for IoT. The biggest point, from a security standpoint, is to develop resilience in order to prepare for unknown threats, assuming that some threats are unstoppable. Rather than trying to defend against every unknown, we need systems that sustain compromise and keep on functioning with minimal inconvenience. It is vital to establish a shared-goal-driven, multi-stakeholder network to develop regulations and security standards for IoT; we need to find a workable balance between ease of use and security. This can only be achieved through the active cooperation of a body of diverse stakeholders, taking into account privacy, human rights, and legal and moral issues.
Taking Action Now
Until international standardization and regulation are realized, organizations should take the following defensive actions:1, 2
- Identify data assets and access paths. Organizations should understand the types of data that wearables and IoT devices are collecting and for what purpose, to assess the data’s value — both to those who use it and those who may want to hold it ransom. They should identify access paths to vulnerable and sensitive data assets and minimize the impact of phishing attacks by using multifactor authentication.
- Secure data collection as well as data analysis points. The IoT data chain starts with the device that collects data, continues through the location where data analysis occurs, and eventually manifests itself in the hands of professionals who can make decisions on the analyzed data. In addition to attacks on the data-collecting device, determined attackers will attempt to compromise the data analysis engine stored in the public or private cloud.
- Reexamine existing security functions through an IoT lens. Companies should factor device context into identity and access management. They should look to cloud service providers to assist with incident response, threat management, and security operations in the cloud, where their data repositories are located. Finally, they need to create policies to address data privacy concerns about data ownership, consent, use, ethics, and liability.
- Isolate IoT devices on their own protected networks. This will prevent compromising the business network when IoT devices are attacked.
- Disable UPnP on routers. UPnP is designed to self-configure when attached to an IP address, making it vulnerable to exploitation. Hackers can change the configuration and run commands on the devices, potentially enabling the devices to harvest sensitive information, conduct attacks against homes and businesses, or engage in digital eavesdropping. Thus, disabling UPnP on routers is an essential means of stemming a cyberattack.
- Use current best practices. Organizations should take extra caution when connecting IoT devices to wireless networks and when connecting remotely to an IoT device.
- Ensure all default passwords are changed to strong passwords. Leaving the default passwords in place will enable a cybercriminal to easily exploit the devices to open doors, turn off security systems, record audio and video, gain access to sensitive data, and so on.
Summing Up
IoT is increasingly used for household appliances, business equipment, and critical services; therefore, securing IoT devices against cyberattacks has become a major concern. IoT implies a massive increase in data being collected and transmitted. The growth in the volume of data creates an inherent increase in vulnerabilities.
To reduce the success of cyberattacks on smart devices, consumers should demand secured appliances, vendors should understand the risks, and international regulators should enforce cybersecurity policies. For industrial IoT security, the security of a whole chain must be ensured.
As bikers are required by law to use helmets, international regulation should likewise enforce “helmets” for IoT devices. At the end of the day, each nation or multinational body must establish rules that represent its values and priorities but collaborate to find common solutions and mechanisms that will serve the interests of all.
Endnotes
1 ”Internet of Things Poses Opportunities for Cyber Crime.” Public service announcement, US Federal Bureau of Investigation (FBI), 10 September 2015.
2 Zetter, Kim. “Why Hospitals Are the Perfect Targets for Ransomware.” Wired, 30 March 2016.