CUTTER BUSINESS TECHNOLOGY JOURNAL, VOL. 29, NO. 12

Every year pundits, hardware vendors, software vendors, consultancies, academics, and even government agencies publish their technology “picks” for the following year. One cannot help but notice that just about all of the lists identify the usual suspects; cloud computing, AI, predictive analytics, wearables, and augmented reality are among about five others that make nearly everyone’s “Top 10.”
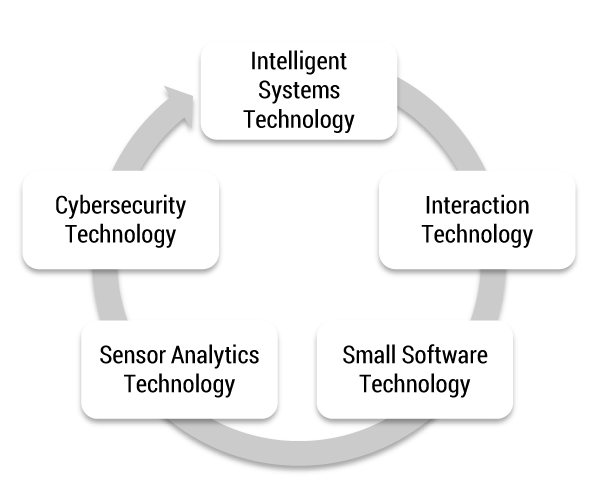
The approach I take here is a little different. I look at clusters of technologies. I do this because of the overlap among the usual suspects and because of the interrelationships among the technologies. The identification of clusters is also useful because it acknowledges the interdependencies among technologies as well as the integration and interoperability required to optimize whole technology clusters and meaningfully impact business rules, processes, and models. In other words, it’s operationally impossible to acquire, pilot, deploy, and support technologies individually because they’re always dependent upon each other and always connected.
The five clusters that scream change in 2017 and beyond appear in Figure 1. The arrow that connects the clusters is extremely understated in its importance. Not only do the clusters build upon each other, but they also depend upon each other for implementation. For example, sensor analytics technology assumes the existence of massive amounts of real-time streaming sensor data and some intelligent processing as well as cybersecurity technology to keep it all secure. Similarly, small software technology requires advanced interaction technology to deliver functionality to consumer and corporate clients. There are also numerous technology standards around sensor interfaces and open APIs that will accelerate the adoption of disruptive technologies. The discussion around clusters here assumes these (and other) standards will evolve.
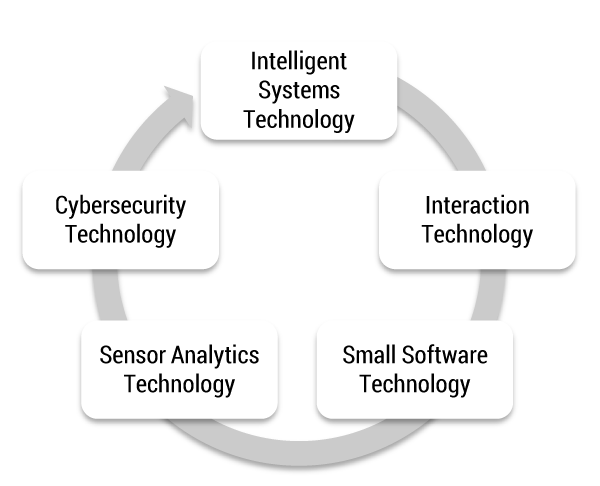
Figure 1 — Five disruptive technology clusters.
Intelligent Systems Technology
Artificial intelligence is now embedded in a wide array of software applications, infrastructures, business rules, processes, and even whole business models. IBM’s Watson is the face of popular AI, but intelligent systems technology encompasses so much more, including:
-
Deductive and inductive inference
-
Deep learning
-
Machine learning
-
Tools and techniques used to represent and process data, information, and knowledge (such as neural network modeling)
-
Applications of the technology to a host of problems, such as conversational speech, language translation, predictive analytics, diagnostics, autonomous vehicles, network management, weapons systems, and augmented and virtual reality, among so many other applications that will affect us all (overtly and covertly)
The development, embedding, and application of intelligent systems technology is accelerating and will continue to do so through 2017 and well beyond. We should track the entire range of this technology, not just the individual pieces, with an eye toward piloting and deploying that range against a set of ROI metrics.
Interaction Technology
The way we interact with all things digital — and physical — is changing. We see and experience content virtually and through augmented reality. We use wearables to track ourselves, our health, our friends, our transactions, and just about everything else we do, see, and hear. Many parents, for example, use smartphone applications to track the whereabouts of their children. We allow location-based services to follow us around, and we buy just about everything with applications on mobile devices. We converse with knowledge bases with relatively crude tools like Siri and Alexa, but within a few years we’ll be having “meaningful” conversations with increasingly intelligent assistants and — eventually — managers.
Assess Your Digital Transformation Opportunities. Plan Your Projects.
Do you understand not only what the "cool" digital technologies do, but also how they do it and the degree of possible optimization-through-transformation they offer? Do you know which of your processes and business models are ripe for transformation? Cutter’s Digital Transformation Readiness Assessment will give you the confidence to move forward with your chosen digital transformation projects.
In addition to voice interaction, we’re well on the way to gesture and other controls that mimic the way we interact with humans. For example, consumers can use gesture control to look at products they might want to buy, and retailers can collect the gestures used to inspect their products and services, such as how often a consumer points to a product over time or how long a consumer lingers on a product icon (versus competing products at which they gesture positively or negatively). Some of this technology already exists for handicapped users of digital technology. Extending it to consumers provides retailers with a new, powerful way to track what their customers are doing with their products.
Small Software Technology
Small software delivered from the cloud is a major technology cluster. The age of monster software applications — like huge multi-module ERP applications — is over. Software is decoupling and shrinking. Even software that stubbornly hasn’t decoupled (yet) is offered in pieces from the cloud to clients who can select the modules they need — and ignore the ones they don’t. For those who want newer, smaller, cheaper packages, there are software vendors (e.g., Zoho and Zendesk) that have reduced functionality to its most useful features.
The small software technology cluster will grow until software becomes like LEGOs that can be assembled and disassembled at will. As the open source API world expands, small software technology will become greater than the sum of its parts. The key trend here is the under-reliance on large integrated software applications and the adoption of smaller, more focused applications accessible on every screen we have.
Sensor Analytics Technology
Ubiquitous sensors capable of tracking, analyzing, and predicting all sorts of activities will soon connect everything. The Internet of Things (IoT) and then the Internet of Everything (IoE) will generate enormous real-time data/information/knowledge streams that must be managed and, more importantly, optimized.
The ubiquity of sensors will change today’s understanding of analytics, especially because they will be “always on” and therefore in real time. The deployment of sensors should be tracked as assiduously as we track advances in data science. The more sensors, the greater the data and analytical requirements, and therefore the greater the number of predictive and prescriptive opportunities, such as the ability to predict threats and generate strategies in response to likely threats in real time.
Companies should invest in expanded analytics with the assumption that data, information, and knowledge will be continuously exploding and that fixed-time, limited variable–driven “analytics” as we practice it today will disappear. It will be replaced by smarter integration across multiple technology clusters. Said a little differently, next-generation analytics will be driven by massively complex multiple regression equations capable of explaining and predicting variance along multiple dependent variables.
Cybersecurity Technology
All of the technology clusters underscore the importance of digital security. There’s the business of security — audits, compliance, policies, and procedures — and the security technology itself. The business side lags the technology side (which lags the device and application sides). All security architectures must continuously adapt while recognizing that the security industry is essentially a reactive one destined to chase solutions to problems it had no idea existed a week, a day, or an hour ago.
Several of the enabling technologies include the broad blockchain family, which in truth is less like a happy family than a set of dysfunctional cousins who seldom if ever communicate — except to solve a really big problem. While blockchain and similar technologies that disconnect and decentralize processes (and assemble them later for clarity) are here to stay thanks to the inherent security features they offer, issues like centralized versus distributed integration and legacy architecture compatibility will persist.
Consequently, there will be significant cooperation required among implementation parties for blockchain to become core to many flavors of transaction processing (beyond cryptocurrency). Some of this cooperation will occur outside of the corporate firewall where digital third parties will inspect and connect transaction components. Some will occur internally as legacy applications are replaced to optimize the technology. The business challenge for blockchain companies will be market share: will blockchain be open and diffuse (“neutral”) oraggressively proprietary and “closed”? The cybersecurity technology cluster requires continuous attention, investment, testing, and implementation within an array of clusters including and beyond those discussed here.
Conclusions
There are several problems with lists of clusters like mine. First, they are never exhaustive. They are also presented at high levels of abstraction. At the same time, they help us break free of bounded definitions of technologies that appear on everyone’s Top 10 lists. The clusters presented here are intended to change everyone’s perspective on emerging and disruptive technologies from definitions and descriptions of individual technologies to a focus on how technologies form clusters that exist in an endless world of interdependencies. This perspective suggests that companies should step back from specific investments in individual technologies and invest instead in multiple technology clusters. It further suggests that those who champion particular technologies — like AI, wearables, and big data analytics — instead think about whole clusters of technologies and how the clusters are greater than the sum of their parts.